Tag Archives: Security
Samsung tweets out malware warning regarding its TVs, but deletes it soon after
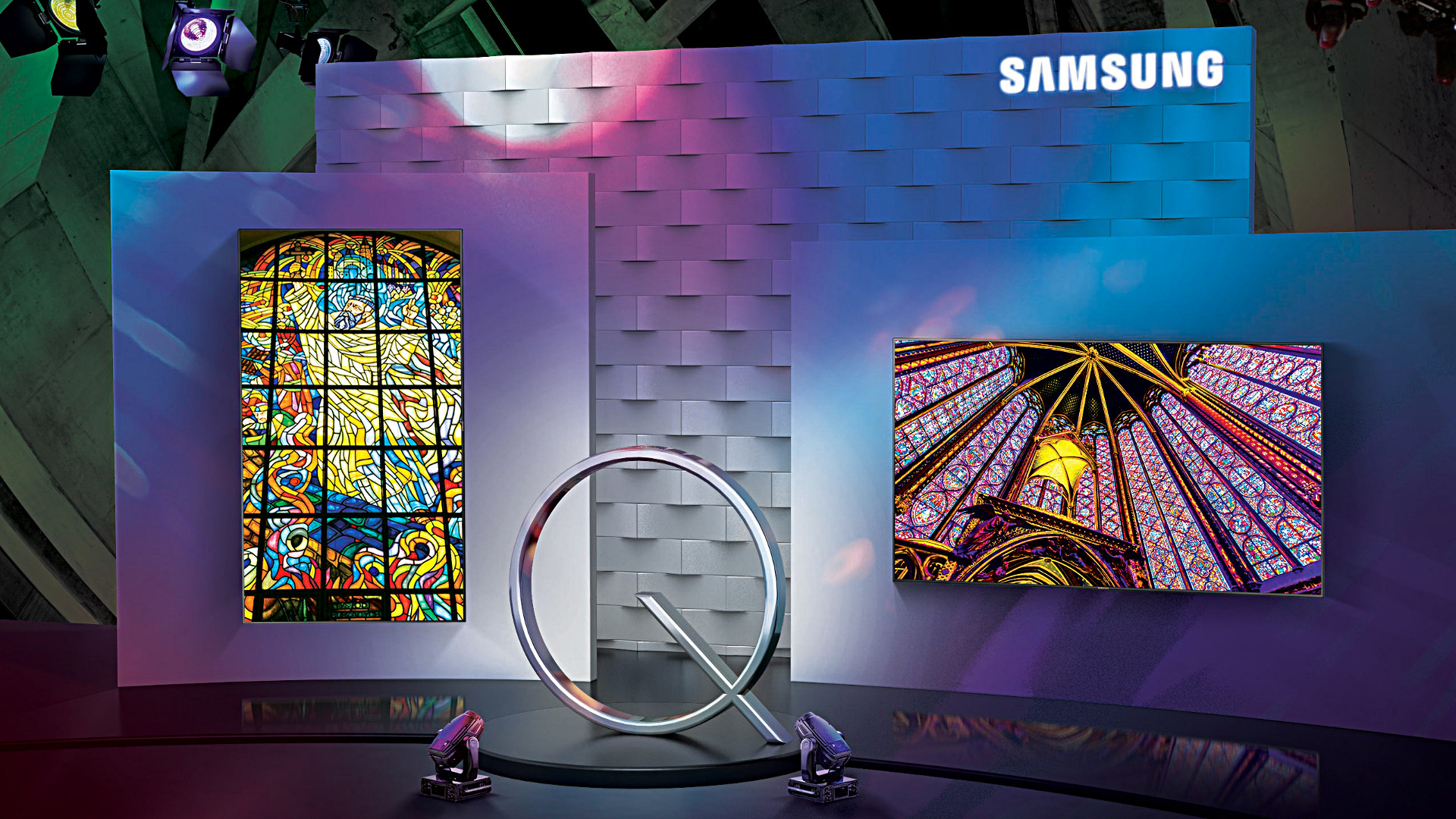
There are two issues here that are of equal importance: First, every single digital device is susceptible to some form of malware or unauthorized access; there is no such thing as a one-hundred percent safe digital device. That being said, some are more susceptible than others. Second, I don’t feel that Samsung deleting the tweet that recommended users scan their QLED TVs indicates anything nefarious; adding another confusing and complex acronym like QLED, which is an incomplete acronym anyway as the ‘Q’ stands for ‘Quantum Dot,’ is much more concerning. While it isn’t the focus of this post, I should add that Quantum Dot technology itself is pretty nifty, as it ostensibly eliminates the need for a backlight and is one step away from the capabilities of OLED, or Organic Light-Emitting Diode, which is one of my favorite technologies when properly applied. You want a paper-thin TV with an image so clear you will fall to your knees and weep? OLED is the way to go; it actually eliminates the backlight since the pixels themselves emit their own light.
That’s an 8K(!) QLED in the header image, but also please remember that if your source video wasn’t filmed in 4K or 8K, it won’t magically appear beautiful on such a TV.
Anyway, back on topic: Samsung claims the reason behind the tweet was simply to inform customers that the option is there and they may want to do the scan once in a while, and I think that’s good advice; I applaud them for that. They later claimed it was deleted because although it was just an advisory tweet, it may raise unnecessary alarms in their customers so they had second thoughts. In a sensationalist world, that also makes sense to me.
The fact is, there is very little malware out there that affects TVs, and those who create destructive software want it to have the biggest impact possible, so writing malware for TVs, even with the installed base Samsung enjoys, isn’t a productive use of the cybercriminal’s time. Additionally, because the TVs run on Samsung’s pseudo-proprietary, lightweight and mostly open-source TizenOS, which is also used in some of its other devices such as smart watches, to provide updatable built-in protection would be trivial.
On top of that, it takes SIXTEEN button presses on a remote to get to the actual malware scan function on a Samsung TV, and the belief is very few people would go through that trouble. They don’t even do that on their PCs when it’s just a few clicks away! That’s anecdotal, by the way: Strangely, I couldn’t find any statistics on how often people actually scan, but if informal surveys in some of my classes are any indication, they don’t do it a whole lot.
But who knows? Maybe TV attacks will become the new undiscovered country for malware authors. Frankly, it doesn’t hurt to scan occasionally, and updating the OS should be standard practice. In Samsung’s case, the best course of action would be to push updates to the TVs on their own, and have them update automatically. If you’d like practical advice and information on security from all aspects, from current federal alerts to info about how to protect your PC and other devices at home, the Computer and Infrastructure Security Administration’s website has tons of it, and putting security into practice is a good idea.
Be safe.
A new exploit for Intel processors?
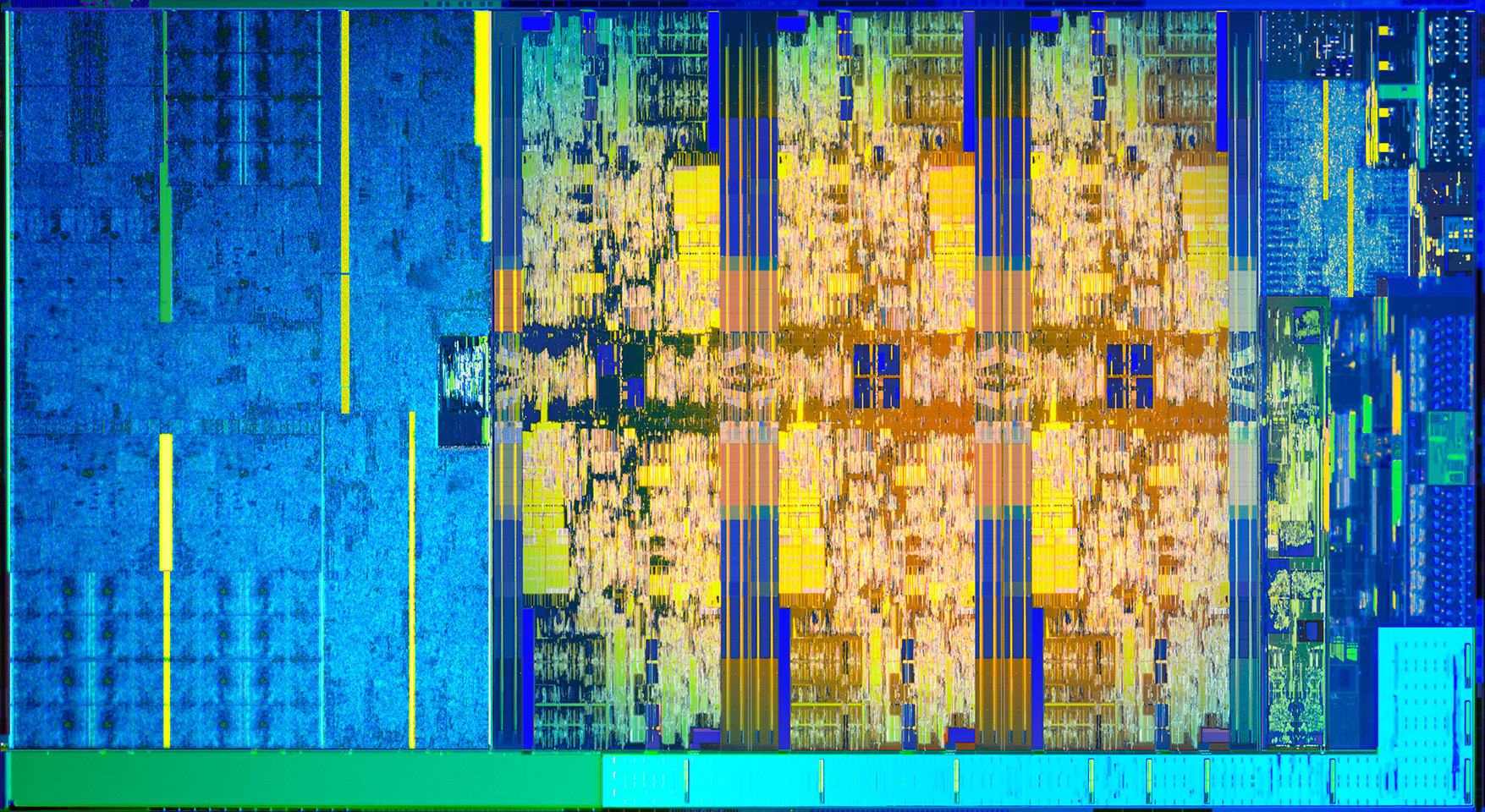
Whether or not this turns out to be a big deal is yet to be seen, but research from collaborators at UC Riverside, Binghampton University, Carnegie-Mellon Qatar, and the College of William and Mary, have discovered a new possible exploit in certain Intel processors that they have dubbed BranchScope – that link will take you straight to the research paper itself. The research is published in the Proceedings of the Twenty-Third International Conference on Architectural Support for Programming Languages and Operating Systems (ASPLOS).
This is a new form of predictive execution exploit, in which the CPU attempts to predict what will happen as the result of a particular instruction, then branch based off of that guess, then guess what will happen as a result of that particular instruction, and so on. It’s the same kind of manner in which a computerized chess game plays chess: Every time you make a move, the game will play out thousands of games as a result of that, trying to guess the moves you will make and the moves it can make in response, and decide on an appropriate next move as a result. It doesn’t make this guess blind, either: In the processor is a component of the Branch Prediction Unit, or BPU, known as a Pattern History Table (PHT) that stores the results of previous operations, and each time a particular branch is taken, the ‘value,’ for lack of a better term, of that branch is increased or decreased. That allows the BPU to be more accurate in its future predictions (Spectre attacked the other part of the BPU, the Branch Target Buffer, which focuses on the result of a branch as opposed to the choice it made).
The exploit, therefore, is to set up selected branches that will modify the PHT and run them so that the PHT will always select one branch over another in a given situation, as well as monitor that the changes to the PHT have actually taken place. These attacks can be used to ensure a particular path is taken when predictive execution happens, and that can be used to divulge information that is otherwise unaccessible, even to the OS, such as key segments, or even provide access to the Software Guard Extensions (SGX), an Intel feature that allows deft software developers to place sensitive or critical data off in protected areas of the CPU cache that should, ideally, be available to none besides the program itself. The whole purpose of the SGX is to prevent bad actors from accessing the data.
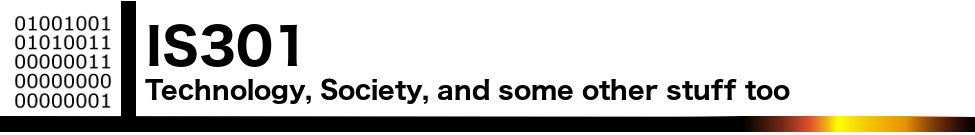
Both the Specter vulnerability and BranchScope as well remind me of the more widely-known and difficult to pull off NOP, or No-Operation, Slide (sometimes Sled or Ramp) type of attack, in which an attacker attempts to bypass a series of CPU instructions such that when an operation does happen, it ends up in a specific portion of memory where malicious code has already been installed and will then be run. These often fail, by the way, and in fact the section of memory that holds the malware will often be padded in front and behind so that the target memory location is bigger and the slide hits by luck; it’s a big shot in the dark. The hex value of the NOP is x90, and if you look at the image below which is tracing CPU instruction executions, you can actually see the slide happening as the series of ’90s’ at the top of the lower left and lower right window (source: samsclass).
This is called a side-channel attack because something is running that shouldn’t be, similar to how loading non-approved, outdated, or unkown-source OSs or apps on a smart phone is considered side-loading.
Predictive execution is complex, the exploits are complex, and as stated earlier, whether or not we see them in the wild is a completely separate issue; the payoff would really have to be worth the effort and I don’t see that being the case unless the exploit was adapted to pair with, say, a trojan horse-style attack, but even then the nature of the returned data would be useless without significant analysis. Knock on wood, but I don’t see this as a common attack vector in the near future.
Has Firefox opted you into any of its studies?
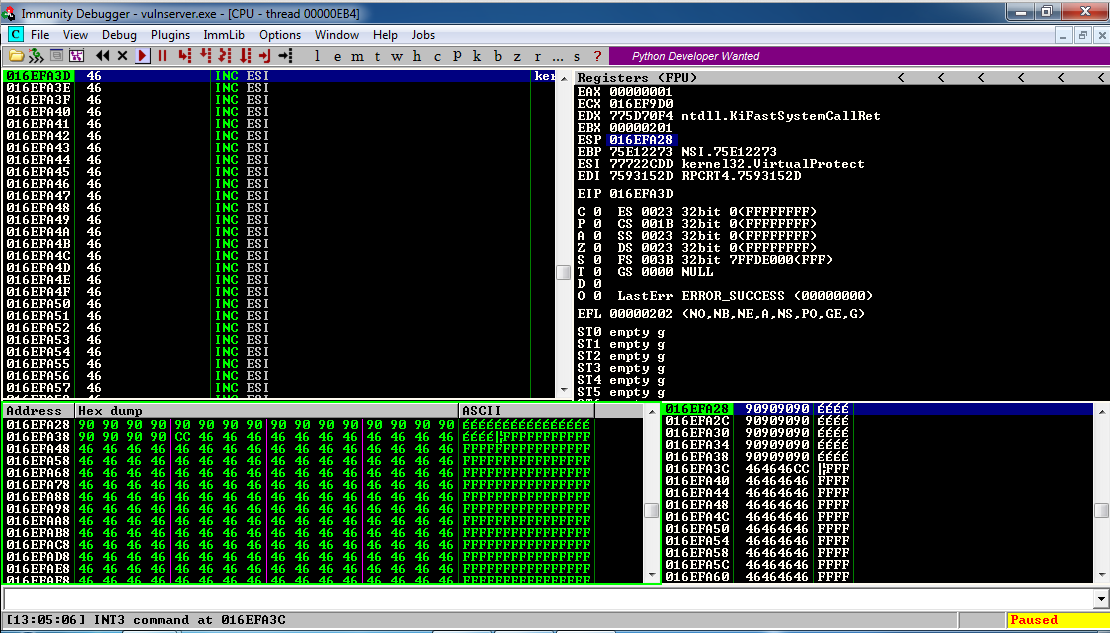
Remember my previous post that talked about the fantastic new version of Firefox, especially the full-screen screenshot capability? I still haven’t adopted it as my main browser, but I was so impressed with th overall changes that were made, I’ve found myself using it more and more; certainly more often than I have in the past. High five for no more memory leaks! Anyway, when I started it up today, it opened to the screen you see below. I was intrigued, especially considering the great improvements they’ve made so far, but as I read through it I also became a little curious. It’s talking about tracking us for usability study purposes, which I’m completely for, but is there anything they perhaps are not telling us? I had no idea the drill down that was about to happen.
This is a new initiative called Firefox Pioneer, which aims to discover how people use their browsers, as well as what they vaguely refer to as ‘health of the web.’ They are careful to note that you need to opt in, which is good, and they are pretty clear about what they will and will not do, and what you can expect in terms of privacy, monitoring, opting out, how private sessions play in, and so on. I do get the feeling they are striving for high-level transparency here and acting in good faith, but perhaps a deeper dive into what they could do is warranted.
I should also mention that while Firefox allows for full page screenshots, that option was not available here. I had to open the page in Opera, save it as a pdf which Opera allows compared to Firefox’s screencap capability, open the pdf in Firefox, and then I could save a full-page screenshot. Very curious, but a triumph for ingenuity.
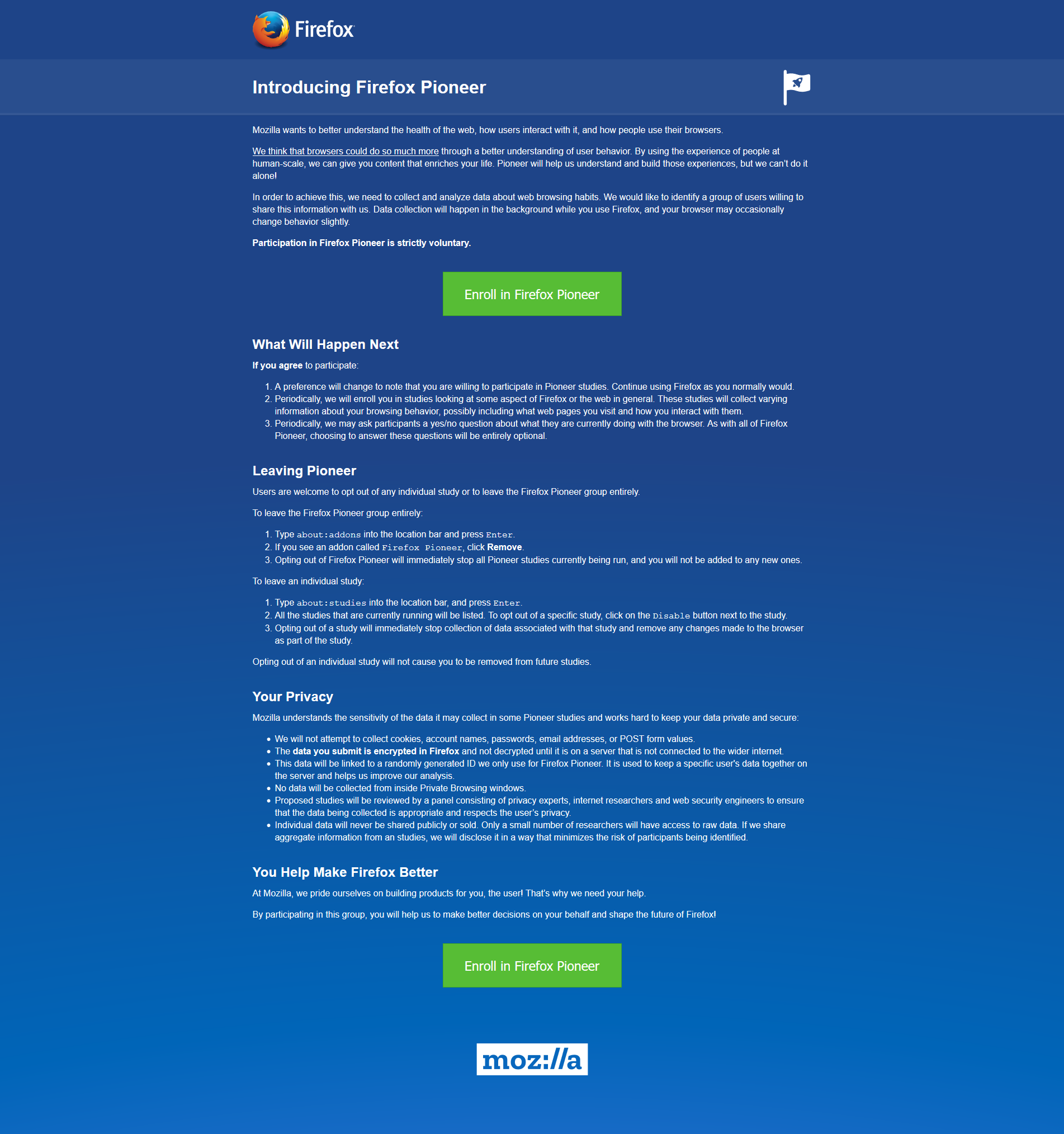
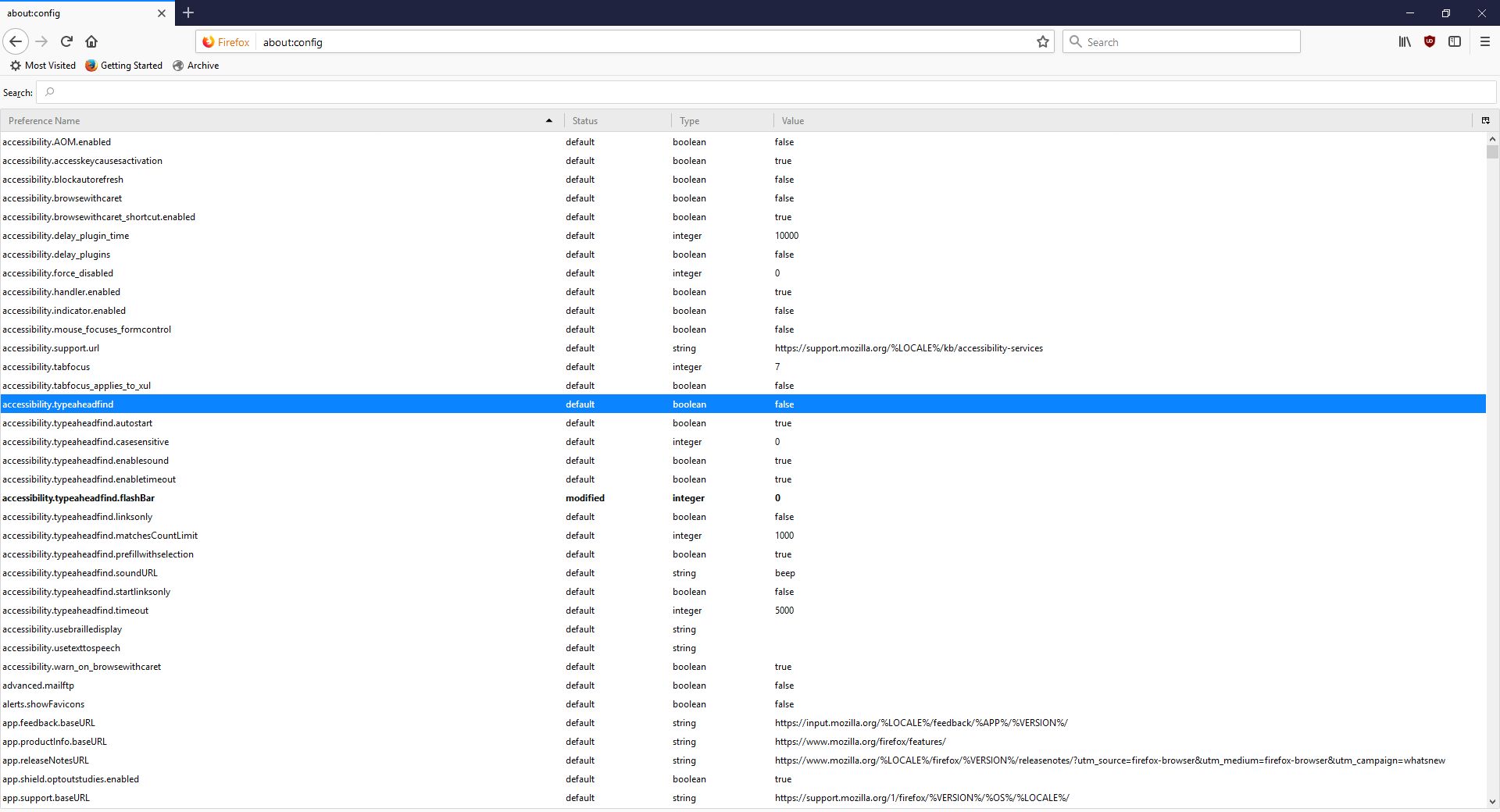
As the page indicates, you can type about:studies into the address bar and see which studies you’re part of, which have completed, and which are available. In fact, you can type about:[topic] into the address bar to discover many interesting things. To see how extensive this capability is, you can see a list at this link. For a real fun time, try about:config – it shows this not at all scary warning, which is really just trying to be funny before letting you access settings. I would normally be for this, however it’s incredibly unclear as to what’s going on if someone isn’t familiar (it fooled me too), especially as it says ‘this application’ and not ‘Firefox.’ Why the pseudo-third person?
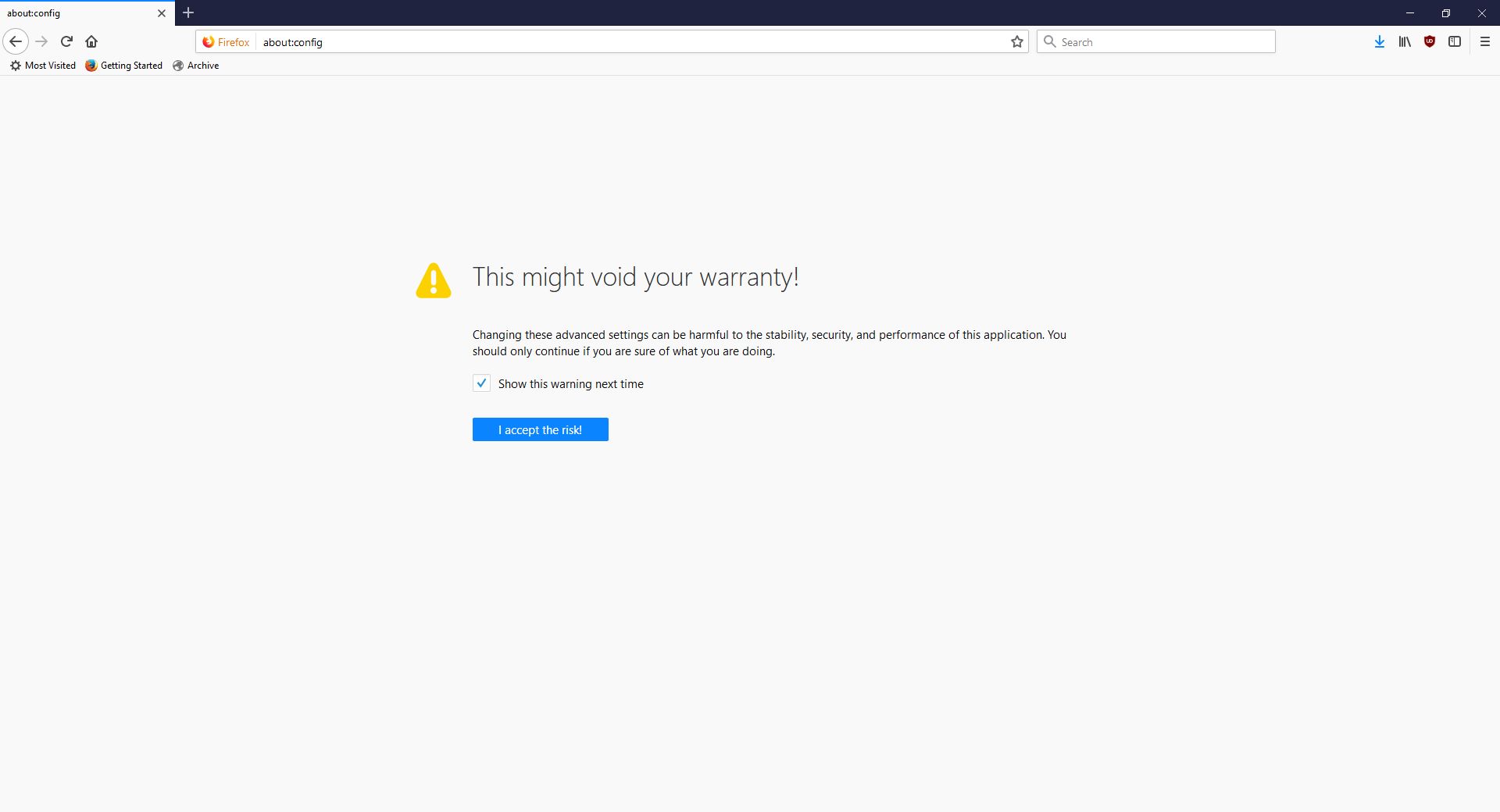
Clicking ‘I accept the risk!’ takes you to a configuration page that isn’t much better in terms of readability or functionality.
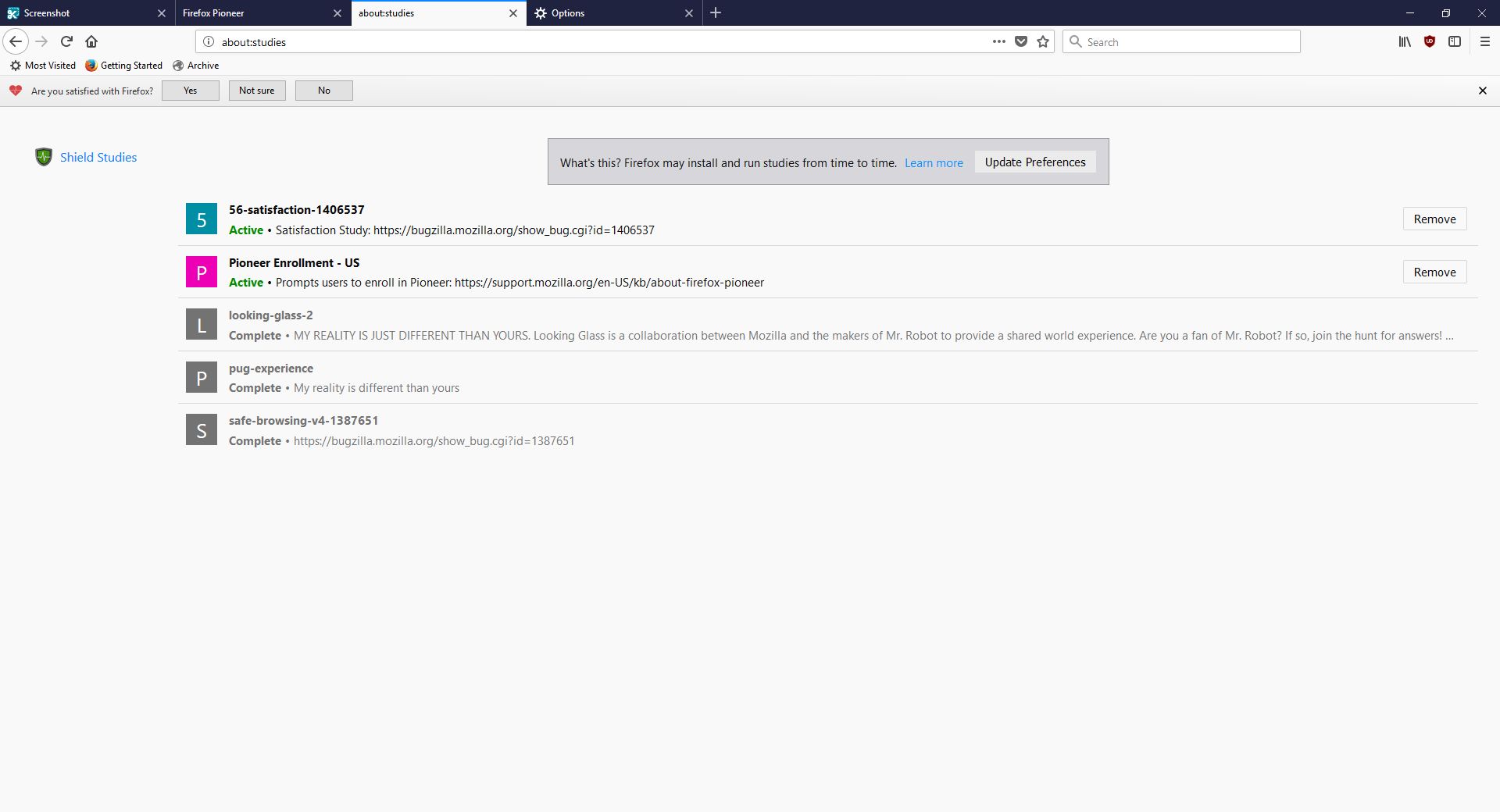
I don’t usually check this kind of thing, but I certainly should. We all know that companies use your data for many things, sometimes not asking first, so it’s important to keep an eye on what any program you’re using is doing. Typing about:studies showed me this screen, which I have to admit got me to wondering what exactly has been going on behind my back:
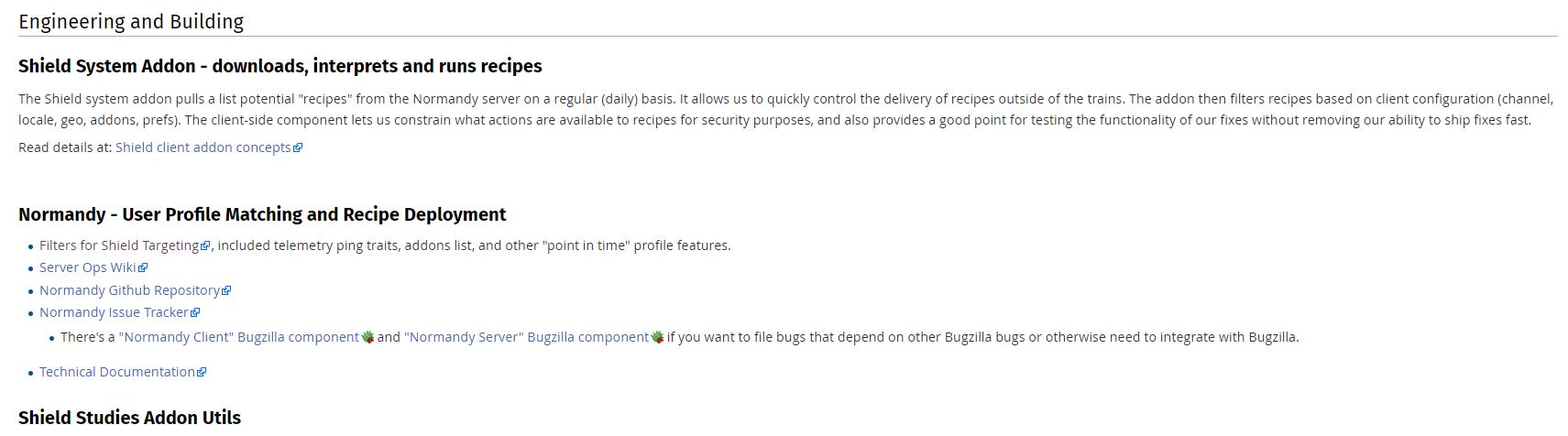
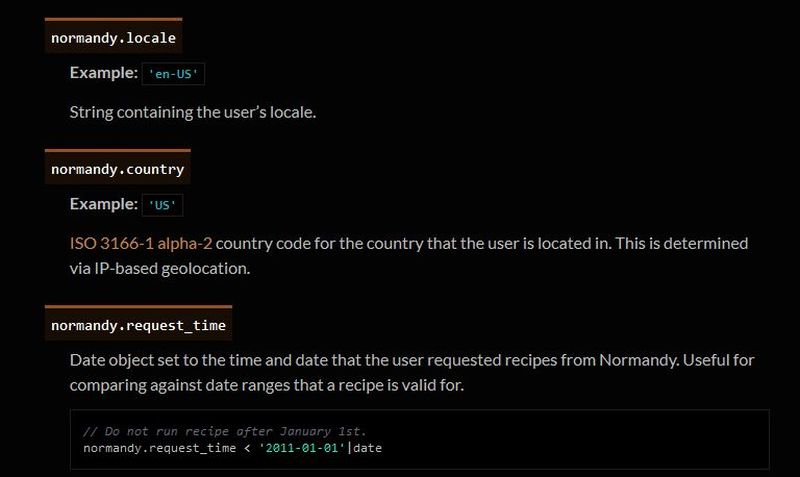
A collaboration between Mozilla and the creators of Mr. Robot? Someone’s reality is different than mine? What is going on here exactly? I clicked on Learn More and was taken to their SHIELD page where I learned all about their SHIELD studies, which they claim are to test new features, however from the original request it’s clear they test more than that. I also can’t figure out why it’s capitalized in such a way; I found no evidence it’s an acronym. A deeper dive led me to another Shield page where it’s maddeningly no longer capitalized, and that’s where I found, towards the bottom, a very concerning entry called ‘Normandy – User Profile Matching and Recipe Deployment.’ I wasn’t completely sure what that meant, but it stood out as sounding perhaps not so good. Just the name is curious: If you’re not familiar, and you should be, Normandy happens to be the location in France where the United States, Britain, Canada, and some of France itself launched the D-Day invasion against the Nazis in 1944. Did you ever see Saving Private Ryan? The opening scene was Normandy. I can’t help but wonder why Mozilla has named this bit of its process in such a way. It may be common knowledge, I don’t know, but it was new – and enlightening – to me.
You’ll notice the first item there, “Filters for Shield Targeting.” That took me to another interesting page, the very first paragraph of which states how certain users can be pegged for recipe execution in their browser, and the means by which that is done has access to location and locale (I’m uncertain as to how those differ in Mozilla parlance). It’s further down the page that you begin to see all the ways you can be tracked and monitored.
I was going to take a screenshot and crop in the sections that were most troublesome, but there are SO MANY it simply was not possible. To give you an idea, here’s what a screenshot of the page looked like in my image editor. I should also add that from a pure design perspective, they are really not using space efficiently.
So there’s a Normandy server, and Normandy is also an object that contains what they call ‘general information’ about the client. Client in a case like this should indicate the browser itself, not the person using it, but separating the two is not so easily done, and as a designer / developer, you’re ultimately trying to learn about the user, about their wants, needs and habits, so you can provide a better product. I have no problem with that, and in fact am completely on board with their Heartbeat initiative, but that is relatively benign.
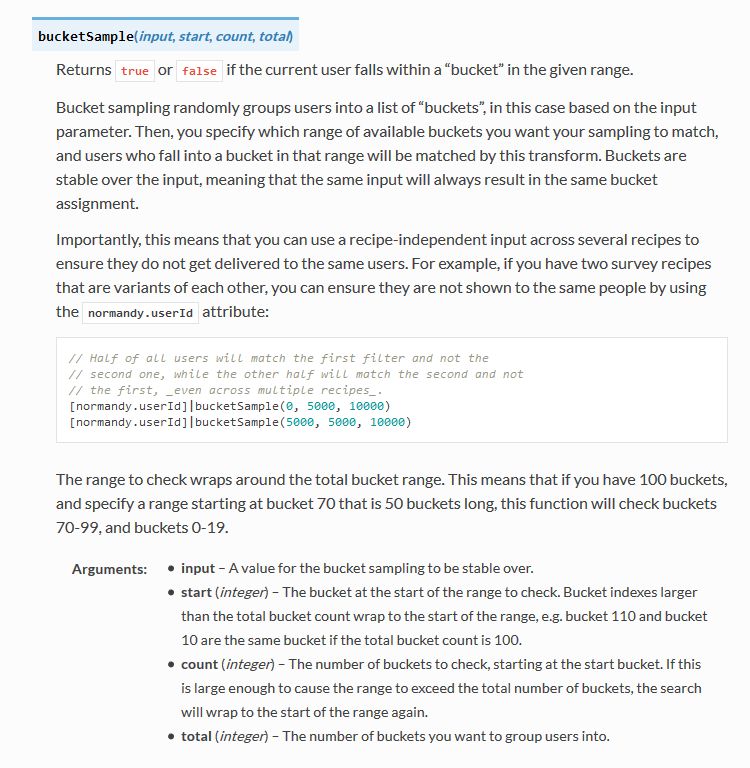
Anyway, back to the above screenshot. They can track a lot, and in the crop below, you’ll see they do something interesting called bucket sampling. I’m intrigued by what this would be used for and how / why / when / etc., so I will have to dig even deeper. I’m guessing it’s some kind of parsing via demographics / usage statistics, but I’m not completely sure. I only found one mention of it on Mozilla’s site, on this page towards the bottom under the heading “Filling the Gap,” but it does lend credence to my assumption. While there’s no formal method known as bucket sampling, it’s something we do, in effect, all the time. I’m looking at you, marketing!
So what does all of this have to do with the study that started this whole post? To be quite honest, this rabbit hole didn’t tell me anything I, or any of you, didn’t already know: It’s very easy to track you online, and not just the websites you visit. Where you are, what software you use, what OS you have, whether you’re a new user or experienced, how many mobile and desktop clients you have, how long you stayed at a site, they can even track if you’ve enabled Do Not Track!
And while this sounds like a conspiratorial, tinfoil-hat rant, I actually am not overly bothered by it. I don’t do anything outrageous online other than download Sega Genesis ROMs, because I’m dangerous and like to live life on the edge. But other than that it’s all pretty boring. My issue was mainly that Mozilla may be opting us in to studies without formally informing anyone, and that I just can’t get behind. This was originally going to be a very short post that I thought could be whipped up in about fifteen minutes, but it instead turned into a downhill slalom.
If you’re interested in reading more about Normandy, Mozilla has a helpful website where you can learn all about it and what it can (and does) do, and it really is an interesting, dare I say fascinating, read. http://normandy.readthedocs.io/en/latest/
Oh, one ore thing – In the latest build of Firefox, Mozilla has also made individual cookie management much more cumbersome. I don’t use that feature a lot, but it is definitely not something people should have to go in to the developer console to access. I love the new Firefox, but this isn’t good – user control should be at the center of all commercial software development. Get it together, Mozilla.
Russian botnet master nabbed in Spain, extradited to US
This is a story that has been ongoing for some time. Pyotr Levashov, a well-known and well-established Russian cybercriminal who was arrested in April of last year (2017 if you’re reading this in the distant future – welcome alien overlords!) while vacationing in Spain, has finally been extradited to the U.S. Apparently cybercriminaling does pay well sometimes. The arrest was based on a formal U.S. Department of Justice indictment against him for, among other things, operating the Kelihos Botnet, a long-running, expansive, global botnet that bombarded the world with all kinds of spam for nonsense like get-rich-quick schemes and enhancement medications; if you’re interested, and you should be, you can read the DOJ press release about the indictment and the actual search warrant that allowed for their infiltration of the botnet.
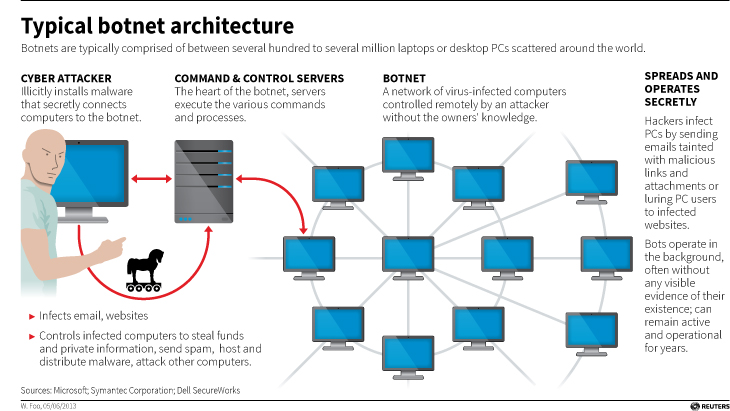
Before we continue, let’s talk about what a botnet is. When malware, or bad software (get it? Mal ware?), is surreptitiously installed on your machine, either through a drive-by attack in which it’s embedded in a Flash ad, or you click on a link or file from a rogue email, or one of many other attack vectors, it will use your machine to carry out tasks without your permission, involvement, or even knowledge. And just to be sure, those tasks it’s carrying out are bad. It can use your machine to send spam, participate in DDoS attacks, store harmful or illegal files, and many other unethical / criminal activities, all without you ever being privy to what’s going on. When that happens, your machine is what’s known as a zombie computer, or more commonly, a bot. Now, imagine hundreds of thousands of these infected machines all acting in unison, for a common goal or under a central control authority. That’s a botnet. Here’s an effective graphic from Reuters that illustrates the architecture of a botnet.
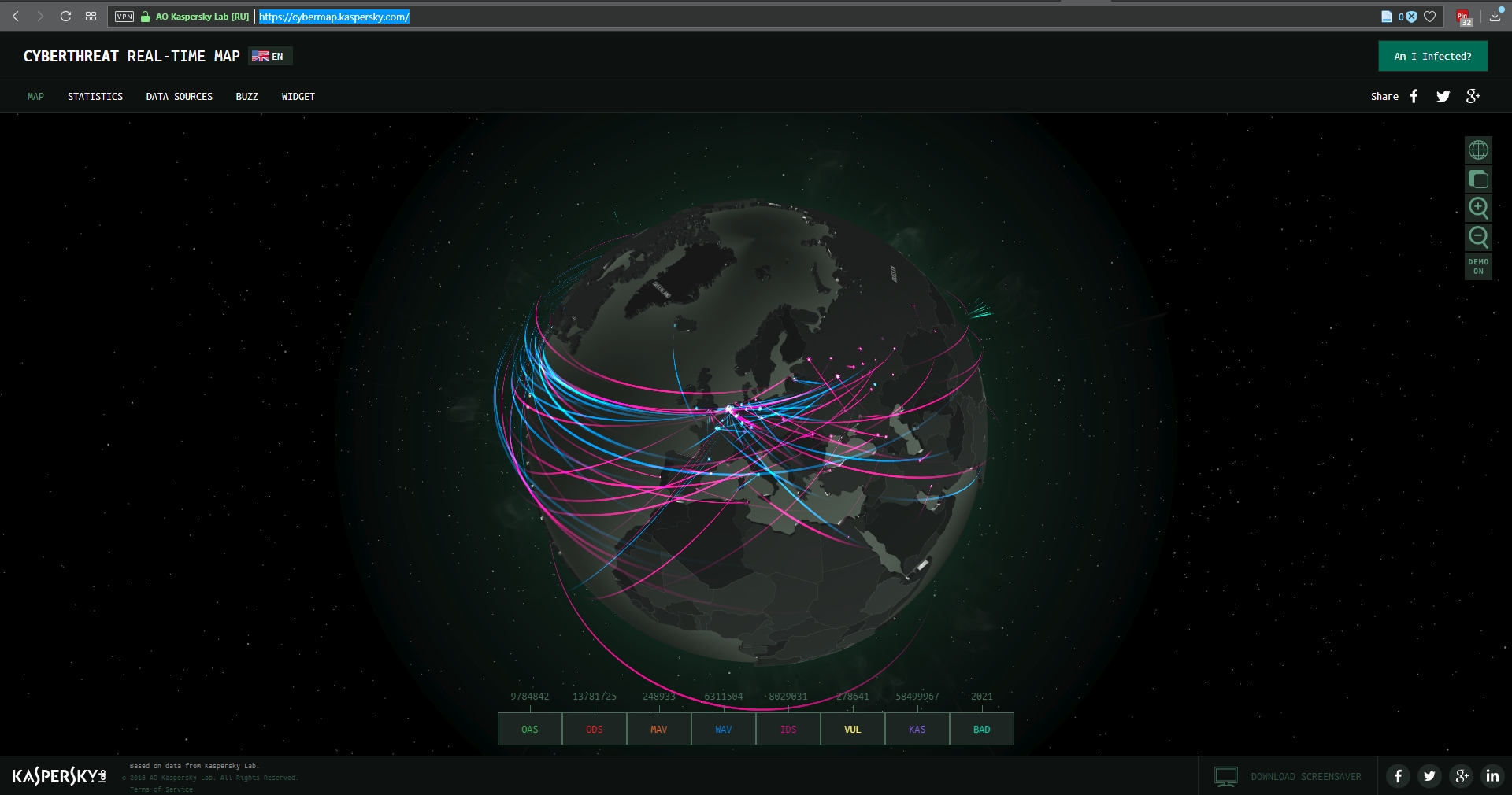
I wanted to embed an interactive map from Arbor Networks that shows real time attacks happening right now, and provides historical data, but their embed code which uses iframes doesn’t work on WordPress. I find it strange a security firm would still be supplying iframe embed codes, but who am I to judge? No matter; there are other sites that provide similar information using their own honeypot networks, such as Kaspersky’s real-time threat map and the well-known Norsecorp map. Actually, I had intended to use Norsecorp’s IPViking map, however it is now run under HP’s banner, although powered by Norse, and I simply couldn’t get it to work in any browser. Their map linked above works beautifully, though.
There are several interesting facets to this case: The first is, this guy has been around a long time and was one of the bad actors behind the Storm botnet that first manifested all the way back in 2007. That botnet was eventually dismantled by the combined efforts of Microsoft, malware firms, and the feds, a partnership and collaboration that continues to this day. We’ll come back to this particular botnet soon, because the architecture of these things is going to become important.
By soon, I mean right now! Another interesting aspect to this case is that the botnet was very sophisticated. It used a hybrid structure that is unusual for this kind of thing. Botnets are typically peer-to-peer, in which all the infected machines communicate with each other to coordinate and carry out their nefarious activities, or they use what’s known as a C&C, or Command and Control server, that oversees the whole thing and controls the botnet form a more centralized location. That allows better control and oversight of the bots.
Kelihos, however, was a hybrid, in which there was a C&C server, but there was also a peer-to-peer aspect as there was some autonomy in the architecture that allowed the bots to continuously update among themselves a list of secondary control servers to which they would report, and those would be directly overseen by the main C&C. This is in direct contrast to the Storm botnet mentioned earlier, which was pure peer to peer. A hybrid network also allows for rapid updates to, and distribution of, associated malware.
That leads to the next neat(?) thing about the botnet: It was aggressively and frequently updated. In fact, when a live sinkholing, in which the bots are redirected to to different targets that can then help track the bots or even deactivate them, took place at a 2013 RSA security conference, a new version of the botnet rapidly took its place which indicated that the creators were prepared for just such an emergency and had pre-planned a contingency.
And this was not just a spamming botnet. Along with pushing spam of both the email and desktop pop-up kind, it also stole bitcoin and targeted banks and other large industry outlets with industry specific malware that could rake in millions of dollars while running undetected. For botnet software, this had a wide range of functionalities, both general and specific, although for all it could do it was not hard to track.
The next interesting aspect of this case is Russia fought vigorously against Levashov’s extradition. Not by attempting to block it, but rather by filing an extradition request of their own based on crimes they say he committed in Russia itself. A smart move, regardless of whether the Russian charges are true or an attempt to protect one of their own, that is a clever way of approaching it. It didn’t work, ultimately, and Levashov is now in U.S. custody, but it was an interesting tactic to counter the original extradition request. Not only that, it has happened before.
A really interesting story all the way around, and I’m curious to see how it concludes. In the meantime, be careful, ensure your OS is up to date and fully patched, be sure you are running up-to-date anti-virus and anti-malware protection, try not to visit questionable sites, don’t activate or respond to emails from unknown sources, use an ad-blocker (uBlock Origin is my preferred choice, and I have no connection to them; purely my own opinion), and just generally practice safe computing.
Intel processors revealed to have major flaw, only addressable by OS updates

UPDATE: I’ve been trying to find out more, but Intel is now claiming it has a fix for the vulnerabilities affecting its chips that it will be rolling out by the end of next week. Details are slim, and I will hold off final judgment of course, but I’ll be surprised if it’s completely effective; these microcode patches can be tricky – it’s not a straight firmware update as it impacts the fundamental operation of the CPU. Additionally, it appears the fixes only address the last five year’s worth of processors. Better than nothing if it works.
Original post follows:
This is bad. It has been announced that Intel processors going back approximately ten years have a major flaw in how they separate the system and software. The details have not been released, but the general idea of the problem is already understood for the most part. To give a very high-level overview of what is going on and the impact of how it needs to be addressed, there is a component of every operating system known as a kernel, that separates the hardware from the software. When a program needs to open a port or save a file to disk or access a printer, or utilize hardware in any other way, it hands off that request to the kernel using what’s known as a system call, and the kernel completes the request (user mode to system mode). The catch is, the kernel is hidden from the program, even distributed in various memory locations to further hide it so that it can’t be exploited by malicious actors; it has to be loaded at system boot, however, in order for programs to use it.
Intel processors, though, use a kind of predictive processing, similar to client side prediction in games, in which a guess is made as to what will most likely happen next. In the case of Intel processors, they try to guess what code will be run next and load it up in the queue, however they apparently do this without any security procedures. The kernel is kept separate because it can contain confidential information such as passwords (which is why you can’t even get your own passwords back and there is no way to recover them if lost), however if the CPU provides no security check when loading up predictive code, it could, theoretically, run code that would ordinarily be blocked, which could then give savvy attackers access to low-level system processes and data.
But wait, there’s more bad news! Because this can’t be fixed with a firmware update or anything similar, OSs have to be written to address the problem. Linux, Windows, and OSX will all require updates that relocate the kernel in memory. Normally, it’s available to each program in their own process, but that will no longer be the case, and having to go back and forth between user mode and system mode in this manner will incur a possibly-significant performance hit on a PC after these updates, estimated by some to be as high as 30 percent.
Again, the details aren’t yet fully known, and the impact isn’t either, but if proven true it could be the worst design flaw I have ever seen. I’ll update when more is known.
Almost all HP laptops have a dormant keylogger

If you have an HP laptop like me, you’ll want to read this. For the second time this year, it turns out that (almost) all HP laptops have a deactivated keylogger hidden in their innards. Before, it was a component of the Conexant audio driver and was actually logging keystrokes, while this time it is part of a debugging component for the Synaptics TouchPad software, something most laptops – not just HP – have, so you might want to take a look or inquire with your manufacturer anyway. HP even states on their patch site, linked below, that the driver affects all Synaptics OEM partners, which means there will be a lot more than just HP laptops affected.
While the keylogger is not activated by default, it could be if someone has administrator privileges and knows which specific registry key to edit, a task that is itself no small matter, as anyone who has done registry edits will know. Interestingly, in an odd take on the situation, some in the security field have noted that if someone has administrator access to a machine, they won’t need to modify a registry key to activate a dormant debugger-based keylogger as they could simply install an actual keylogger. The counterpoint is that the driver-based keylogger, because it’s actually part of an integrated debugging / tracing function, would be harder to detect and leave less of a trace than a full-blown logger, so it would be a less intrusive and more opportune choice for those looking to listen in; there’s a built-in excuse for why it might be doing what it’s doing.
That’s assuming it’s detected, of course. The fact is, detecting them is notoriously difficult. Things have gotten better, but even the best antivirus program has trouble identifying them, and that’s even more true of one that’s operating at the system level – you might want to try a scanner that looks for keyloggers specifically. Since nothing is easy, those types of programs are few and far between because of the difficulty in detecting the logger in the first place. The one most often recommended is KL-Detector, but I’m not convinced of its effectiveness and definitely uncertain of the last time it was updated, which is critical in security software. While it will run on Windows 10, the only systems it explicitly confirms are Windows 2000 and XP, not something that gives me confidence as to its currency. Plus, it’s not a removal tool, only a detector. I don’t know why it’s so often recommended.
Physical keyloggers are easy – check where your keyboard plugs into its port. No additional device, no keylogger. Honestly, these are practically obsolete and were mainly used when keyboards still plugged into PS/2 ports, but don’t be fooled – USB physical keyloggers are out there, but are not commonly used because the chance of discovery is high.
It must also be noted that while there are obvious nefarious uses for keyloggers and that is why we generally hear about them, they have valid uses as well. If you are a parent who’s concerned about what your kids are doing online, a keylogger might be one option, especially these days. If you’re conducting a legitimate investigation, a keylogger is an option and has been used in the courtroom, both successfully and unsuccessfully. And, as alluded to above, they have valid testing and debugging uses. It’s similar to peer-to-peer sharing software; we mainly hear about how it’s bad, but it can also be very useful.
In a way it’s better than the previous time this happened because the keylogger is not active, but it’s worse because so many more models are impacted. HP acted right away and issued a patch, although if you received a Windows Update in the last couple of days you should be fine as well. If you’d like to be doubly sure, you can check HP’s patch site to download a patch for your model. There are a lot of links, so you’ll need to know your exact model.
Pentagon may ban Kaspersky AV line

Bloomberg and others are reporting that the federal government is concerned about the widespread use of Russia-based Kaspersky Lab‘s antivirus products, which have been in widespread use around the world for almost two decades. High-ranking U.S. officials, including current acting FBI Director Andrew McCabe and Director of National Intelligence Dan Coats, who both gave congressional testimony related to Kaspersky, have voiced their concerns even going so far as to say they would not feel comfortable using the product in their own homes.
Times have certainly changed. I have used Kaspersky extensively over the years and never had an issue with it, nor any reason to suspect that, because of its being developed in Russia, it was anything other than an effective AV product. Speaking of which, it really is, at least in my personal experience, and apparently that of others; it’s very well-regarded. Tom’s Hardware lists it in their #2 and #3 spot of best AV products for 2017. PCMag.com lists it as their #5 choice. Windows Central has it as #3. Howtogeek noted it, along with BitDefender, found 100 percent of threats and even lists it as ‘the absolute best.’ Even MacWorld lists it as #5 for Mac protection. Their Wikipedia page, a site to which I am usually loathe to link, lists a slew of additional achievements and accolades. I have recommended it for years and have never balked once at doing so. Perhaps I’m not enough of a conspiracy theorist, maybe I should be more of one, but I find it hard to believe a company with almost half a billion users worldwide, the respect of the computing community, and the list of accomplishments it has as a product and company, would compromise their robust integrity by colluding with a nation of any sort, not just Russian.
On the other hand, as much as it hurts me to say it, such are the times in which we live. In the video on this ABC News page, which incidentally is where you can see brief bits of the FBI and National Intelligence Directors giving their congressional testimony, is an image of Kaspersky founder Eugene Kaspersky with Vladimir Putin. I personally don’t think that’s an indicator of anything; many business people meet with members of their respective governments, and others, all the time. To me personally, absolutely nothing stands out about this picture. No evidence has been provided as to why exactly Kaspersky now suddenly poses a threat, other than the current political climate. As all my students know, I never allow politics to seep into my classes unless it is absolutely necessary, however, we are where we are at this moment in history, and Kaspersky is an enormous juggernaut of a (Russian) company. Although they have offered to turn over their source code in an effort to prove their legitimacy, I suppose the security machine here in the States would like to be safe rather than sorry.
I, on the other hand, being the eternal optimist that I try to be, will for now continue to recommend them and hope they have not been compromised by political pressure. If you are concerned, there are many, many other options from which to choose. The aforementioned and previously linked BitDefender is solid, as is Avast, I’m not a huge fan of AVG, another long-time stalwart that I used to use in the past, but it does work well, overall, and its reviews are generally strong.
Continuing on the security thing, you should also use a dedicated anti-malware package, and nothing equals MalwareBytes. I use it on Mac, PC, and mobile, and recommend running it daily; bad things can happen in an instant.
I am completely OK with this
Now this I have no problem with whatsoever, although it hints at a larger issue. Researchers at University College London have discovered a dormant but massive Twitter botnet comprised of an estimated 350,000 fake accounts that does nothing but tweet out random quotes from Star Wars novels.
They discovered it quite by accident while taking a pure random sample of English-speaking Twitter accounts. It’s important to note the importance of this sampling method, as other methods of sampling might bias the results in favor of those accounts that are more active or have more followers. Their one percent sample resulted in approximately six million accounts.
Once their random sample was complete, they plotted the geographic distribution of these users, and they discovered something curious. Many of the tweets formed an almost perfect rectangle along latitude/longitude lines, including open, uninhabitable places like frozen tundra and bodies of water. They conjecture the shape was deliberate to mimic where English-language tweets are most likely to originate, and hide them within the clutter of legitimate Twitter users Tweet flood.
Upon further investigation, the researchers found another surprise. All these Twitter accounts did was tweet out random passages from Star Wars novels. They also never retweet, they send out very few tweets (around ten total) and list ‘Twitter for Windows Phone’ as the tweet source. As much as I hate to say it, that is also likely a ploy to get them to stay under the radar as much as possible because of that platform’s significantly low user base.

It’s not Twitter, but Darth Vader actually posted this on Instagram. Seriously. He doesn’t even care about that stormtrooper behind him.
Using a machine-learning word association approach (a ‘classifier,’ although classifiers are not limited to word association), it found that actual users had a very wide distribution of word choice, while the bots used words almost entirely related to Star Wars. Additionally, the platform percentages were evenly distributed for the most part among real users while the botnet was one hundred percent Twitter for Windows Phone. When the numbers are examined, the botnet is easy to see.
The authors then discuss the implications. Clearly, a dormant, low-activity Star Wars-themed Twitter botnet is not a big deal. However, if the creator decided to reactivate the botnet in order to create a spam network, send malicious messages, or use it for other nefarious purposes, they could. I personally don’t believe that will happen as it likely would have already, however as the authors also note, the botnet went out of its way to stay under the radar.
One of the things I find most interesting about it all is that the authors hint they found another, even more massive Twitter botnet using the same approach, which they will be reporting on at a later date.
Really interesting stuff, and touches on the impact of social media, machine learning and AI, cybersecurity, and geolocation/geotagging just to start (as well as the curious motivations of this particular botnet’s creator). I very much recommend giving it a read.
Destroy your stuff with just a USB stick

Hey, now this sounds fun! Want a simple, effective, and inexpensive way to destroy your expensive stuff and all the data on it? Well do I have good news for you! Now, with just a simple USB stick you can blow up damn near any digital device with a front-facing USB port (meaning publicly accessible, it doesn’t actually matter which direction the thing is actually facing. An important distinction).
The USB Kill will charge itself from the USB’s power supply, then discharge itself back into the port, over and over again until the host device is broken. Of course they say don’t use it for malicious purposes, but come on…why else would we want one of these things? Oh right – ‘testing’ purposes.
To be fair, everyone knows USB ports are a haven for malicious attacks, they’re the mosquito-breeding stagnant pond of digital devices, a very easy way to infiltrate a system or exfiltrate (steal or lose) its data.
It’s a pretty nifty device, in and of itself, and another interesting point they make is that only Apple devices are protected against this type of attack out of the box. Everyone else, well, look out (also, it might not destroy the data, and if it doesn’t, then NSA-approved bulk erasers are for you!).
WordFence to the Rescue!
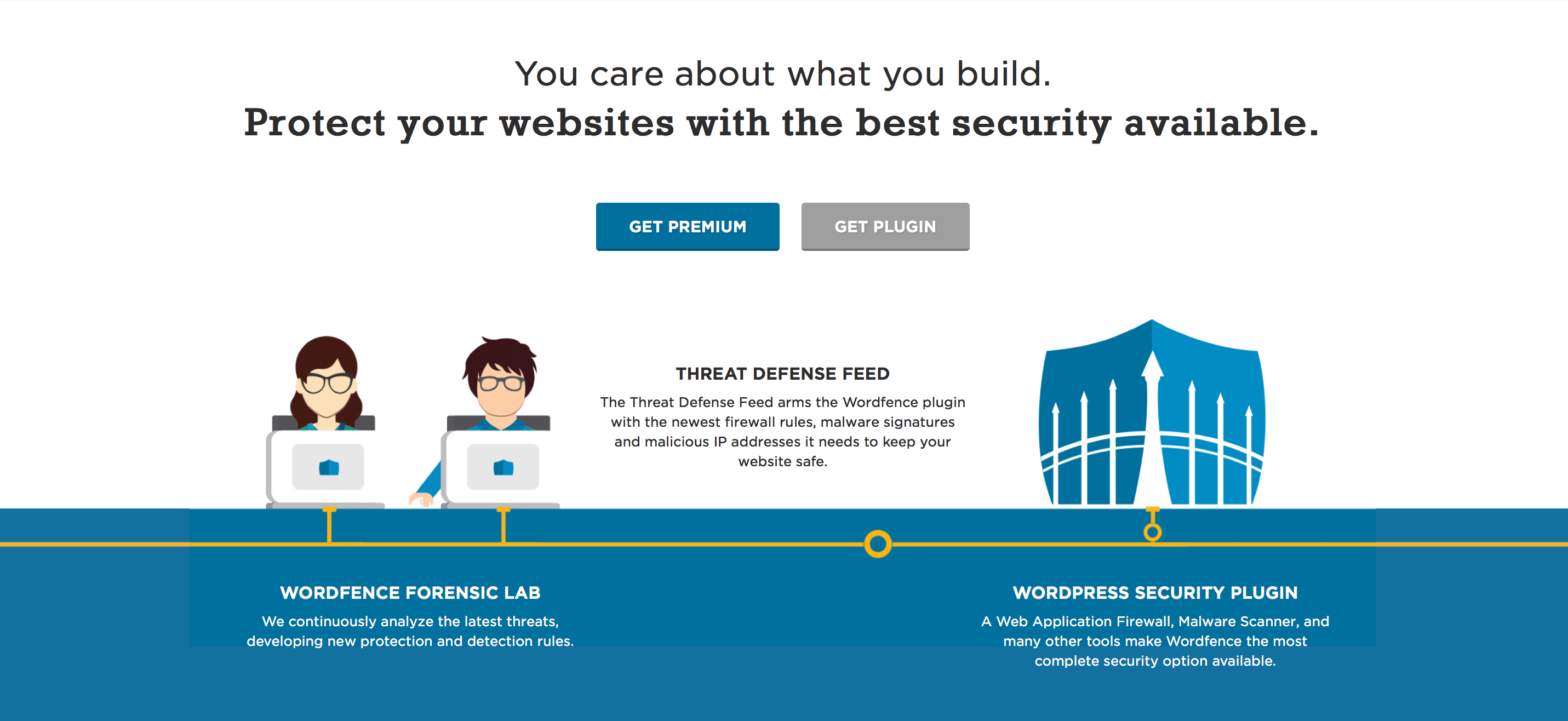
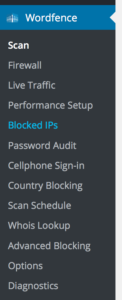
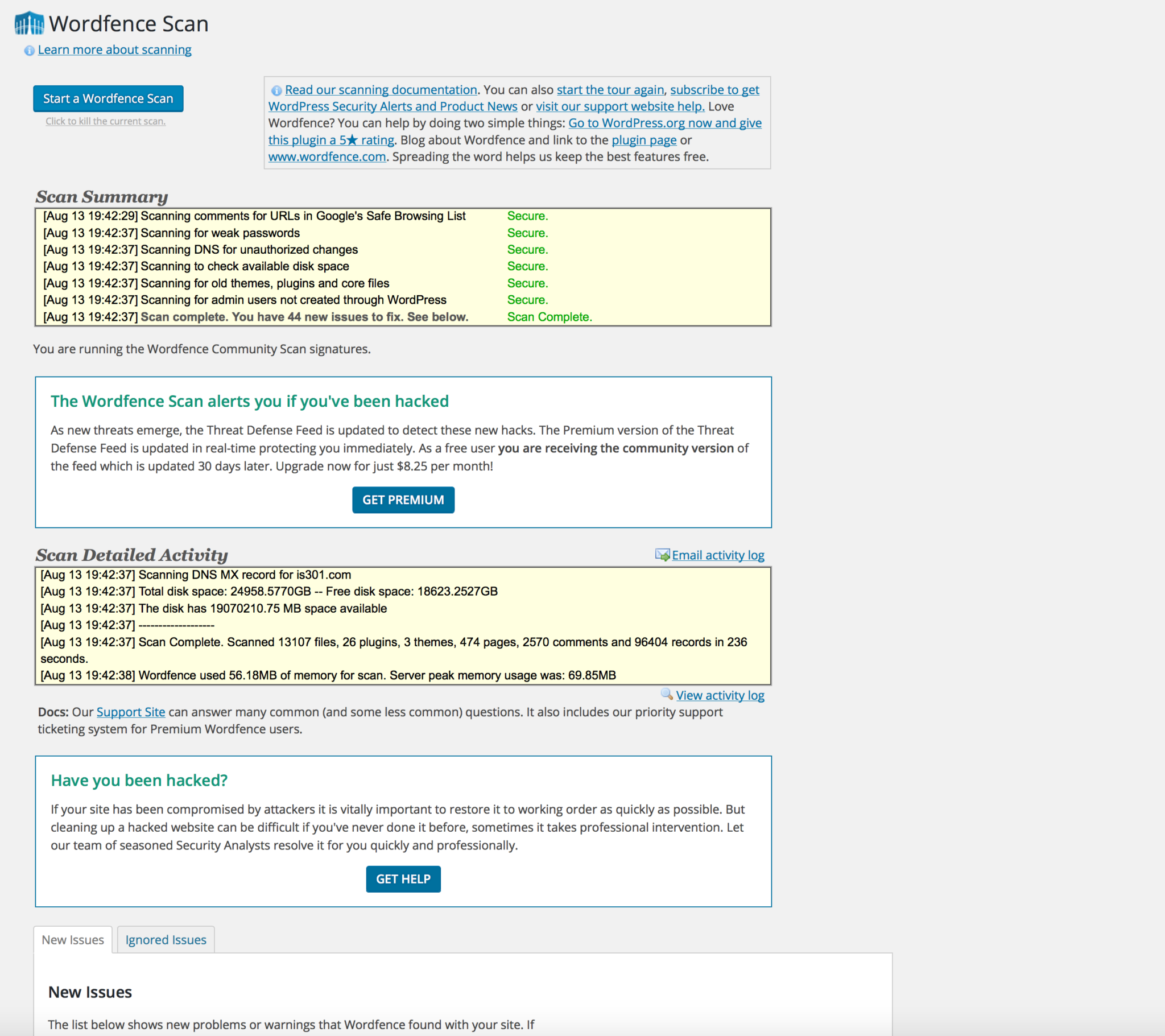
Over the weekend, I added WordFence security to the site. WordFence is a free (with premium option) service that provides backend security and monitors a WordPress site and prevents all sorts of bad things from happening. It has a slew of options and services that can be configured in any way a user would like, providing some peace of mind.
As you can see, the services and options it provides are many:
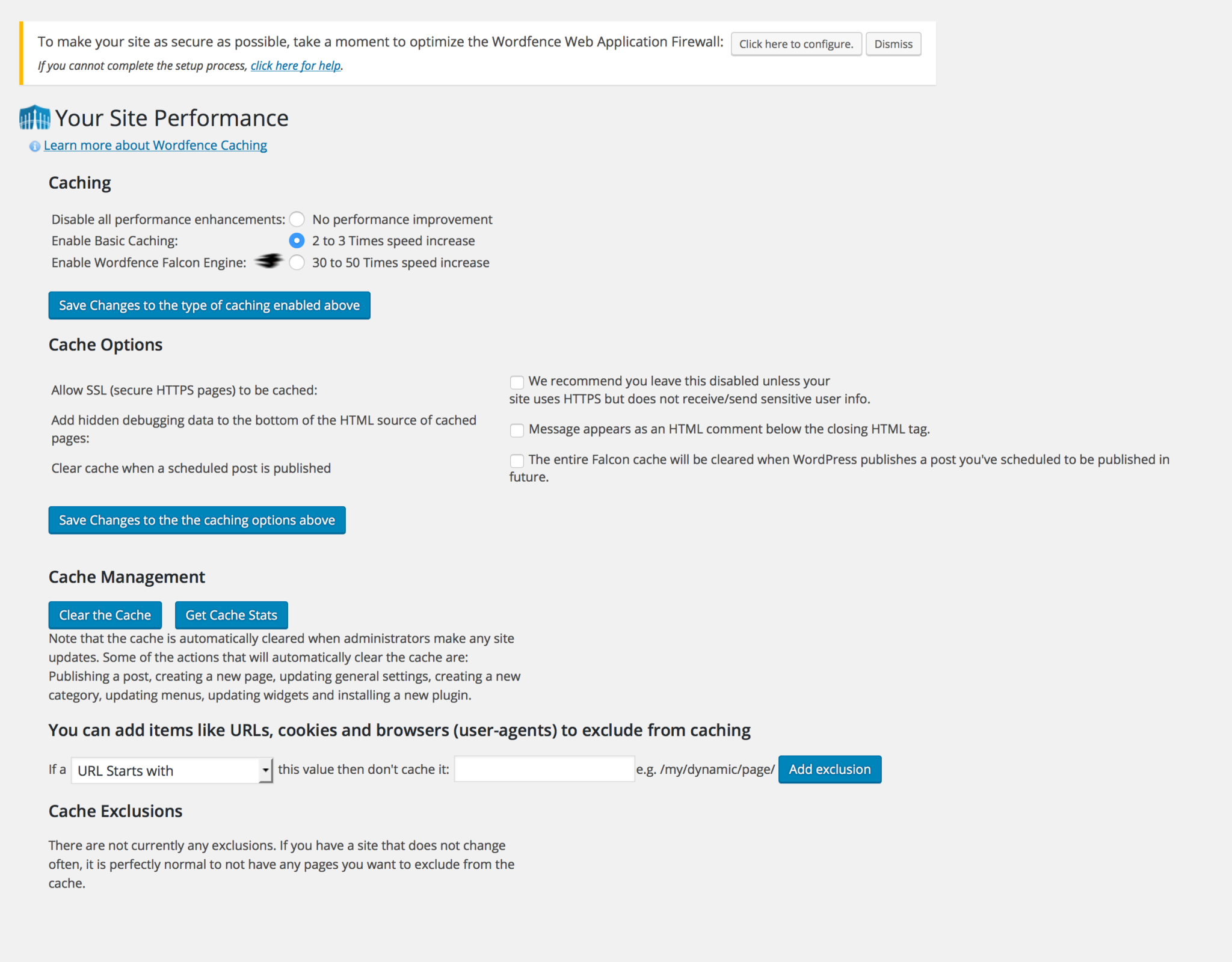
It has, for example, a firewall that prevents unwanted actors from gaining access to your site, however as with any good firewall you can whitelist sites or block sites as you see fit. It also claims it learns as time goes on, however I’m not able to test that at this time.
I’ve had this site for several years now, so as you can imagine with all the posts and photos and links there are a lot of potential hazards, and the service did a complete scan to be sure everything was on the up and up. It found a potentially malicious link in one of my posts from two years ago, and although the link was simply giving credit for a header image and not actually malware, I deleted it anyway. It scans everything for malware, the aforementioned malicious links, and any other problems and ranks what it finds in terms of its severity. I’m glad to say this site, to paraphrase Tangina Barrows, is clean.
There are many, many, many options. This kind of thing can often result in a performance deficit, although I haven’t noticed any slowdown at all. On a curious side note, I was asked to download my .htaccess file before WordFence scanned my site and implemented itself which I thought was strange. If you’re not familiar, .htaccess is an Apache-specific file placed in a directory of a website that specifies some site functionality, such as redirects or even password access without having to modify the server settings; WordPress itself states that it “uses this file to manipulate how Apache serves files from its root directory, and subdirectories thereof,” and .htaccess functionality cascades to all subdirectories (it can be overridden with another .htaccess file in a subdirectory, but that’s for another post). Why they wanted me to download that they never specified, but I did and ended up not needing to worry.
Another interesting thing about the .htaccess file is that it has been around FOREVER!
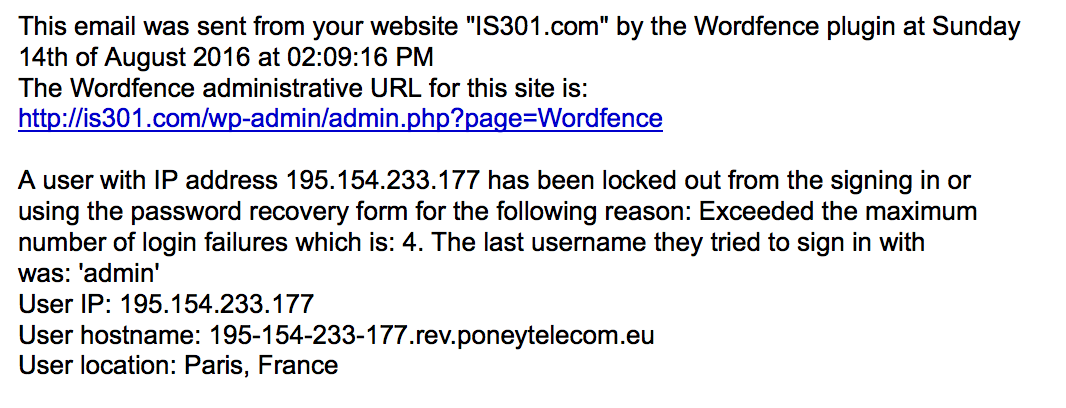
So with that sidetrack out of the way, the site is now more secure than ever, WordFence is running in real time, and I’ve already received some emails telling me about the login attempts they’ve blocked (from both Germany and France – I’m worldwide!) and how smoothly my site is running. I’m very happy with it so far. If you have a site and are interested, it’s very easy to install and can be done from the ‘install plugins’ section of the WordPress backend.